In this topic I will discuss how to configure VTP on our switches. From this point onwards I will try to use our topology from the interVLAN topic.
We will configure Switch C and switch B as our VTP servers and Switch A as our VTP client.
These are global settings we will used on our three switches: (Note these are case-sensitive)
VTP Domain: Cstark
VTP Password: cisco
Switch A:
configure terminal vtp domain Cstark vtp password cisco vtp mode client
Switch B:
configure terminal vtp domain Cstark vtp password cisco
Switch C:
configure terminal vtp domain Cstark vtp password cisco
No need to specify the server mode. By default switches are servers. If required to change between client/transparent the command is vtp mode server.
On Switch C we will create four VLANs 10, 20 30 and 40. VLAN 10 and 20 are already configured, We’re just naming them here:
configure terminal vlan 10 name Marketing vlan 20 name IT vlan 30 name Finance vlan 40 name HR
If we go to Switch B and switch A and issue a show vlan command we will notice the two VLANs have automatically been created for us:
Switch B:
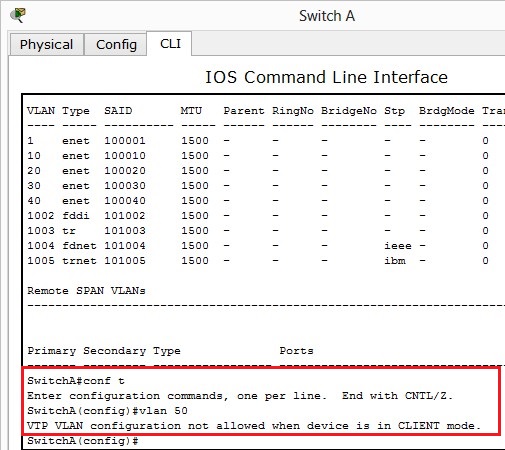
Lets try and configure VLAN 50 on Switch A:
We are unable to do so! VTP is working correctly.
VTP Pruning isn’t supported as of writing this on Packet Tracer version 5.3.3. The command would be vtp pruning under global configuration. This will stop the advertisement of unused VLANs to other switches. This cannot be set on clients only servers but will propagate down to VTP clients. You could instead use switchport trunk allowed vlan #vlan under each interface to manually prune – this does give you much greater control.
I haven’t configured a transparent switch, the command to make a transparent switch is vtp mode transparent. A transparent switch will forward VTP information but has its own local database.
Verifying:
The following commands will help with verifying VTP on each switch:
- show vtp status
The show VTP status command will show what VTP version is running, how many revisions, operating mode and VTP domain name.
The VTP version is in fact 1, I’m not sure why its showing 2. Trying to force VTP version 1 results in the following:
Switch C(config)#vtp version 1 VTP mode already in V1.
- show running-config – to verify vtp is configured correctly
- show vlan – will show the VLANs that have been created
Troubleshooting:
- show vtp status – checking revision numbers are consistent across switches will indicate if VTP is working correctly
- show vtp password will display the password if you’ve forgotten it
- Ensure Domain name, version and password are the same – these are case sensitive!
- If you cannot add a VLAN, the switch may be configured with client instead of server
- VTP only supports 255 VLANs